Cyber Monday 2024! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Cisco Exam 200-201 Topic 6 Question 80 Discussion
Actual exam question for
Cisco's
200-201 exam
Question #: 80
Topic #: 6
[All 200-201 Questions]
Topic #: 6
Refer to the exhibit.
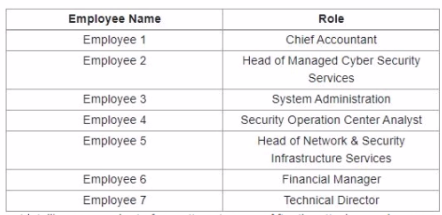
A suspicious IP address is tagged by Threat Intelligence as a brute-force attempt source After the attacker produces many of failed login entries, it successfully compromises the account. Which stakeholder is responsible for the incident response detection step?
Suggested Answer:
C
Delmy
7 months agoNana
7 months agoBelen
7 months agoDelmy
7 months agoCarey
8 months agoVilma
8 months agoRhea
8 months agoMelvin
8 months agoVelda
8 months agoColette
8 months agoMozell
8 months ago