Cyber Monday 2024! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Cisco Exam 300-215 Topic 10 Question 73 Discussion
Actual exam question for
Cisco's
300-215 exam
Question #: 73
Topic #: 10
[All 300-215 Questions]
Topic #: 10
Refer to the exhibit.
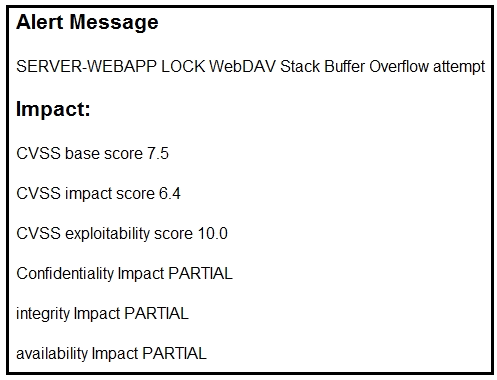
After a cyber attack, an engineer is analyzing an alert that was missed on the intrusion detection system. The attack exploited a vulnerability in a business critical, web-based application and violated its availability. Which two migration techniques should the engineer recommend? (Choose two.)
Suggested Answer:
C, E
Alline
6 months agoJarod
7 months agoTawny
7 months agoAlline
7 months agoBenedict
8 months agoGilma
8 months agoAlpha
7 months agoAdelle
8 months agoFrance
8 months agoJennifer
8 months agoEloisa
8 months agoMelissia
8 months agoShaquana
8 months ago