Cyber Monday 2024! Hurry Up, Grab the Special Discount - Save 25% - Ends In 00:00:00 Coupon code: SAVE25
Eccouncil Exam 312-96 Topic 1 Question 20 Discussion
Actual exam question for
Eccouncil's
312-96 exam
Question #: 20
Topic #: 1
[All 312-96 Questions]
Topic #: 1
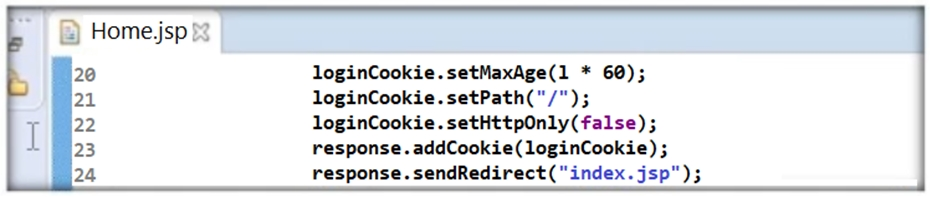
Thomas is not skilled in secure coding. He neither underwent secure coding training nor is aware of the consequences of insecure coding. One day, he wrote code as shown in the following screenshot. He passed 'false' parameter to setHttpOnly() method that may result in the existence of a certain type of vulnerability. Identify the attack that could exploit the vulnerability in the above case.
Suggested Answer:
B
Ammie
4 months agoAmina
3 months agoFreida
3 months agoDomingo
3 months agoJospeh
3 months agoCarisa
5 months agoEdna
5 months agoBrittni
4 months agoLorean
5 months agoWilda
5 months agoColette
5 months agoHui
4 months agoPearline
4 months agoEllsworth
5 months agoMarylyn
5 months ago